What is it?
The Cyber Resilience Act (CRA) is a mandatory EU regulation that sets standardized cybersecurity requirements for all "products with digital elements." It ensures that any hardware or software sold in the EU is built with security-by-design and remains protected throughout its entire lifecycle.
What you need to do
Mandatory Reporting (by 11 September 2026): Establish internal processes to report exploited vulnerabilities and severe security incidents to EU authorities.
Full Compliance & CE Marking (by 11 December 2027): Ensure all products meet "secure-by-design" standards and vulnerability management requirements. After this date, non-compliant products can no longer be legally sold in the EU.
By 2021, the annual cost of cyberattacks (opens new window) reached a staggering €5.5 trillion, driven largely by vulnerabilities in everyday hardware and software. To close these security gaps, the European Union has introduced a landmark regulation: The Cyber Resilience Act (CRA).
This legislation marks a fundamental shift in how digital products are sold in Europe. By mandating "security-by-design," the CRA ensures that cybersecurity is not an afterthought, but a legal requirement throughout a product’s entire lifecycle. From initial development to long-term maintenance, manufacturers must now prove their products are resilient before they can touch the EU market.
Building on the 2020 EU Cybersecurity Strategy (opens new window) and the NIS2 Directive (opens new window), the CRA introduces a standardized "CE" marking system to give businesses and consumers peace of mind. If a product has digital elements, the CRA likely governs it.
What is the Cyber Resilience Act (CRA)?
The Cyber Resilience Act is a regulatory framework that establishes baseline cybersecurity standards for all Products with Digital Elements (PDEs)—covering both hardware and software—sold within the European Union.
While previous guidelines were often voluntary, the CRA makes security a mandatory prerequisite for market entry. It specifically targets two systemic failures in the digital market:
- Inadequate Security: Many products are released with known vulnerabilities and lack long-term update support.
- Information Asymmetry: Consumers and businesses often cannot distinguish between a secure product and a vulnerable one.
Who is Considered a "Manufacturer"?
The CRA uses a broad definition to ensure no product falls through the cracks. According to Article 3, a manufacturer is any natural or legal person who:
- Develops or manufactures a PDE.
- Has a PDE designed or manufactured by others and markets it under their own name or trademark.
- Distributes the product, whether for a fee or free of charge.
CRA vs. NIS2: What’s the Difference?
The CRA is frequently described as the "companion" to the NIS2 Directive. While they work together, their focus is different:
- NIS2 regulates the entities (companies) that provide critical services (like energy or health). It often exempts small businesses based on size or revenue.
- The CRA regulates the products themselves. There are no exemptions based on company size. If you sell a digital product in the EU, you must comply.
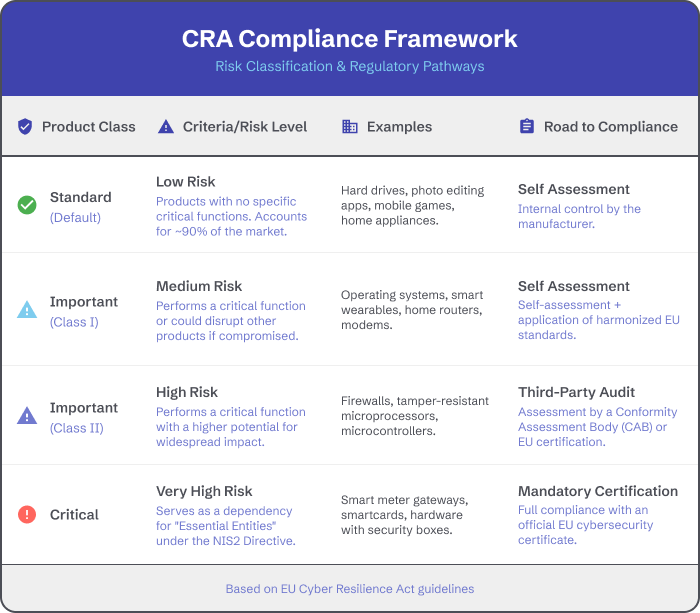
Product Risk Categories & Compliance
The CRA classifies products into three tiers based on their risk level and the potential impact of a security breach. While the baseline security requirements are the same for everyone, the assessment process (how you prove you are compliant) becomes more rigorous as the risk level increases.
Why the CRA Matters for Equipment Manufacturers
The Cyber Resilience Act casts a wide net. Under the official definition, if you develop, manufacture, or even outsource the design of a Product with Digital Elements (PDE) to sell under your own trademark in the EU, you are a manufacturer.
This applies to hardware giants and app developers alike. Whether you are building an industrial sensor or a mobile app for iOS or Android, the legal responsibility for security now rests squarely on your shoulders.
Key Compliance Obligations
To enter or remain in the EU market, manufacturers must shift from a "ship now, patch later" mindset to a "Security-by-Design" framework. This involves three core pillars:
1. Transparency & User Information
You are now legally required to provide users with clear, accessible instructions regarding:
- Vulnerability Handling: Where and how users can report security issues.
- Security Environment: The intended secure usage setup and the product’s specific security properties.
- Lifecycle Support: Detailed information on how long the product will receive security updates.
- Secure Usage: Step-by-step instructions for the secure commissioning, daily use, and decommissioning of the product.
2. The Declaration of Conformity
Before a product touches the market, manufacturers must draft a formal EU Declaration of Conformity. This document acts as a "security passport," tracking the product’s compliance and providing essential manufacturer data to regulators.
3. Mandatory Technical Documentation
You must maintain a comprehensive technical file that includes:
- The Software Bill of Materials (SBOM): A nested inventory of every software component and dependency within your product.
- Cybersecurity Risk Assessment: Documentation of potential threats and the mitigations you have implemented.
- The EU Declaration of Conformity: Proof that the product meets all CRA standards.
CRA Penalties & Enforcement
The Cyber Resilience Act is enforced through mandatory reporting and strict oversight by national authorities—such as the National Cyber Security Centre (NCSC) in Ireland.
The "24/72/14" Reporting Rule
Starting 11 September 2026, manufacturers must report actively exploited vulnerabilities and severe incidents via the EU’s Single Reporting Platform.
- 24 Hours: Initial "early warning" notification.
- 72 Hours: Detailed update with a severity assessment.
- 14 Days (Vulnerabilities): Final report once a fix is available.
- 1 Month (Incidents): Final report following the initial 72-hour notification.
Consequences of Non-Compliance
Failure to meet these obligations can lead to severe financial and operational sanctions:
- Administrative Fines: Up to €15 million or 2.5% of annual global turnover, whichever is higher.
- Market Restrictions: Authorities may order a mandatory product recall or prohibit the sale of future products within the EU.
- Reputational Risk: Public disclosure of non-compliance can result in the loss of the CE marking, effectively barring the product from the European market.
CRA Key Dates & Actions
All core obligations of the Act including full secure-by-design and vulnerability management requirements will be fully applicable from 11 December 2027, after which non-compliant products cannot be sold on the EU market.
However, from 11 June 2026, the CRA's rules on notification of conformity assessment bodies will apply. In addition, the reporting obligations of manufacturers for actively exploited vulnerabilities and severe incidents, will apply from 11 September 2026.
To learn more about the EU Cyber Resilience Act and to understand more about how to implement it into your business, as well as upcoming key dates please visit the European Commission website (opens new window).
Assess Your CRA Readiness
The Cyber Resilience Act marks a turning point in the digital market, shifting cybersecurity from a "best practice" to a strict legal requirement. For equipment manufacturers, the road to December 2027 requires immediate action in product architecture, lifecycle planning, and documentation.
If you are building or scaling connected solutions, you don't have to navigate these complexities alone. Choosing a platform that prioritizes security-by-design can significantly accelerate your path to compliance.
Compliance Inherited with Davra
Davra maintains the highest global security standards, ensuring our partners can focus on innovation rather than infrastructure. Solutions built on the Davra inherit our robust security and compliance controls, including SOC 2 Type II, ISO 27001:2022, and DOD-IL5 Readiness.
By leveraging Davra’s compliant infrastructure, manufacturers can simplify their own certification journeys and ensure their products meet the rigorous demands of the European market.
Further Reading & Next Steps
To dive deeper into the specific implementation standards and technical requirements, we recommend visiting the official European Commission’s CRA Implementation Guide (opens new window).
Are you ready for the CRA? Contact our compliance experts today (opens new window) to learn how our platform can help you secure your products and maintain EU market access.







